The dApp user experience problem is well-documented yet rarely addressed at the infrastructure layer. Blockchain automation is what changes that. You know how Netflix just works? You click play, and the show starts. No one thinks about the content delivery network spinning up, the authentication handshake, or the adaptive bitrate algorithm adjusting to your bandwidth. The technology is […]
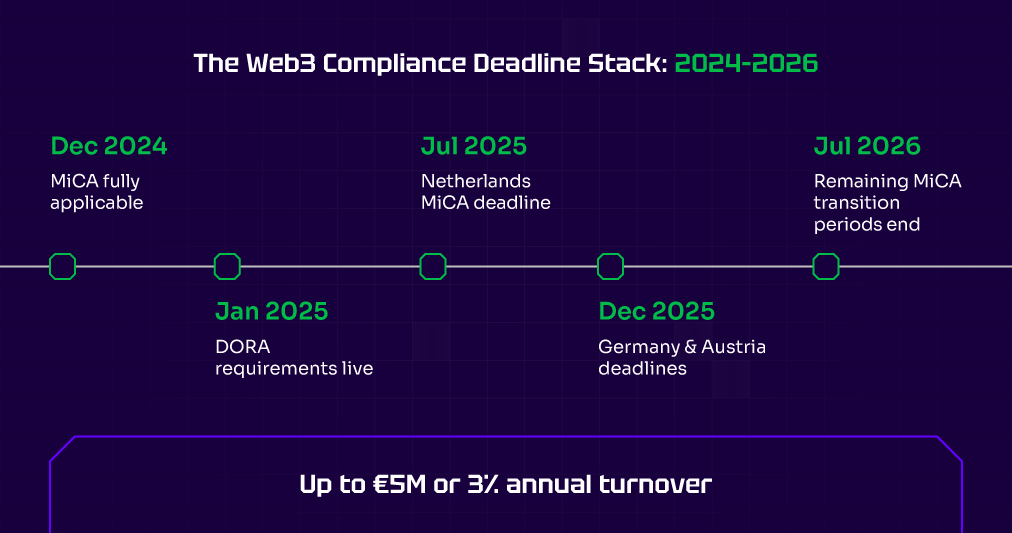
Read MoreMiCA (Markets in Crypto-Assets) became fully applicable in December 2024. The Travel Rule has no grace period. DORA requirements started in January 2025. DORA adds a second compliance dimension beyond transaction monitoring. Under DORA, financial entities including CASPs must demonstrate operational resilience, maintain ICT risk registers, and report major incidents within defined timeframes. Kwala’s event-driven architecture supports DORA operational monitoring by detecting anomalous contract behavior, logging system events with tamper-evident timestamps, and routing incident alerts to your DORA response workflows — giving compliance teams the audit evidence DORA requires. And most compliance teams still manually copy transaction data into spreadsheets.
As of January 2026, France’s top financial regulator, AMF, said that a third of crypto firms are unresponsive ahead of the EU deadline.
Everyone else faces mounting pressure to meet compliance deadlines that keep arriving. Non-compliance carries penalties up to five million euros.
For enterprise teams building on-chain infrastructure, Web3 compliance automation is no longer optional it’s the only way to keep pace with regulatory velocity.
Web3 compliance automation is not about replacing compliance officers. It is about giving them systems that match the speed of on-chain activity. Manual processes worked at low volume. They break when thousands of transactions flow through daily.
Here is what that automation layer looks like in practice and why compliance teams building it now will operate with confidence while others scramble to catch up.
Why Manual Compliance Breaks at Blockchain Scale
Your platform processes thousands of transactions across multiple chains each day. Each one potentially triggers reporting requirements. Each wallet interaction might need sanctions screening. Each large transfer could require Travel Rule data exchange.
The compliance officer reviewing 50 transactions per hour cannot review 5,000. The spreadsheet tracking 100 users becomes chaotic at 10,000.
The solution to this mismatch is on-chain compliance automation. As the blockchain data is already transparent and timestamped, every transaction sits on a public ledger ready for audit.
What teams lack is an automation layer that connects raw events to compliance workflows. Understanding how blockchain events trigger automated actions is the foundation for building compliance workflows that run without manual intervention.
How On-Chain Event Triggers Power Crypto Regulatory Automation
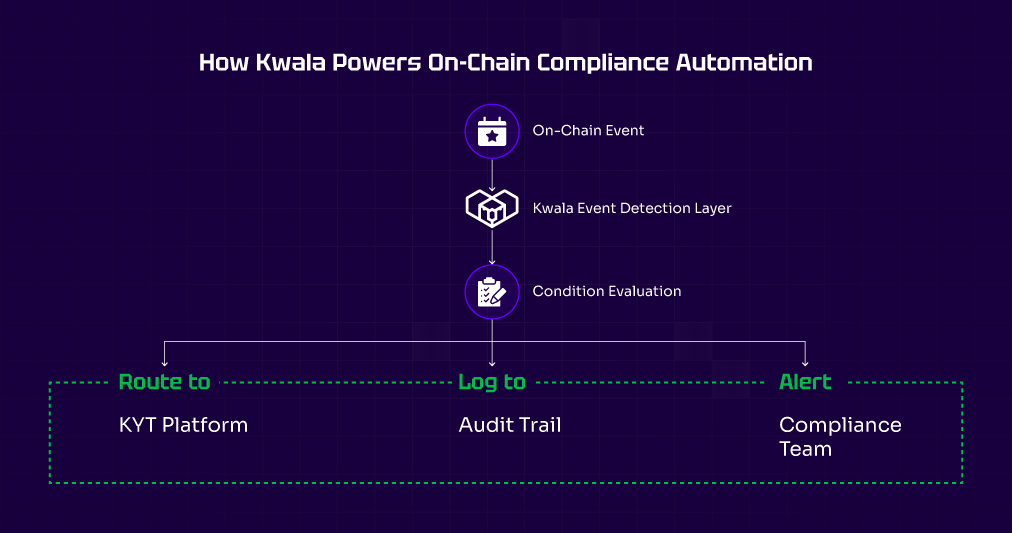
Crypto regulation automation through Kwala works through event-driven workflows. You define what to monitor, set conditions, and configure actions.
Transaction threshold monitoring
Under the Travel Rule, transfers exceeding €1,000 require originator and beneficiary data exchange between virtual asset service providers. Under MiCA, reporting obligations kick in at defined thresholds for asset-referenced tokens and e-money tokens. Manually tracking these thresholds across thousands of daily transactions is operationally impossible at scale.
A Kwala threshold monitoring workflow addresses this directly. You define the trigger on your token contract’s Transfer event with a value condition matching the regulatory threshold. When the event fires, the workflow pulls transaction metadata, formats it according to the required data standard, and routes it to your compliance review queue or directly to your Travel Rule provider via API. The entire detection-to-routing cycle completes in seconds without a compliance officer reviewing raw blockchain data.
Set up triggers that fire when transfers exceed regulatory limits. The workflow detects the event, pulls sender and recipient data, and routes information for compliance review automatically.
Suspicious activity detection
Compliance involves pattern recognition beyond simple thresholds. Each of these patterns maps to a configurable workflow logic in Kwala. Rapid inflow/outflow detection uses time-window triggers if a wallet receives and sends above a threshold within a defined period, the workflow fires. Dormancy-to-activity spikes use baseline comparison: wallet address with no activity for 90+ days suddenly executes five transactions in an hour. Structuring detection monitors for multiple sub-threshold transactions from the same address within a rolling window a classic smurfing indicator.
These aren’t hypothetical configurations. They’re the same behavioral patterns AML teams screen for manually today, automated as event-driven workflows that run continuously without human monitoring overhead.
Build workflows that detect these patterns and alert compliance teams for enhanced review. The same event-driven workflow logic that powers transaction notifications extends directly to compliance monitoring the trigger mechanism is identical, with compliance-specific conditions and routing layered on top.
Building Compliance Workflows That Scale Across Jurisdictions
Enterprise blockchain systems must handle overlapping compliance requirements across jurisdictions, asset types, and regulatory frameworks simultaneously a complexity that manual processes cannot manage at scale.
Travel Rule compliance requires exchanging originator and beneficiary information for qualifying transfers.
Configure workflows that trigger on qualifying events, pull KYC data, format according to requirements, and route for counterparty exchange.
Kwala’s workflow configuration follows the same declarative structure across all use cases define the contract, define the event, define the action. Compliance workflows add conditional logic for threshold matching and jurisdiction routing on top of that base structure.
A Kwala Travel Rule workflow operates in four stages. First, the trigger detects a qualifying transfer on your monitored contract. Second, an API action calls your KYC provider to pull originator identity data. Third, the workflow formats the payload according to IVMS 101 data standards. Fourth, it routes the formatted data to your Travel Rule solution provider Notabene, Sygna, or any provider with a REST API endpoint for counterparty matching and transmission.
The workflow handles the detection and routing. Your Travel Rule provider handles the counterparty protocol. Your compliance team handles the edge cases that require human judgment. Each layer does what it does best.
Stablecoin-specific rules under MiCA treat asset-referenced tokens and e-money tokens differently. Configure separate workflows for each token type with appropriate reporting triggers and formatting requirements.
Connecting Kwala to Your Existing Compliance Stack
You already have compliance infrastructure in place:
- KYC providers handling identity verification
- Transaction monitoring platforms scoring risk
- Case management systems tracking investigations
- Regulatory reporting tools generating filings
The last thing you need is another isolated system.
Kwala supports Web2 API calls as workflow actions. When on-chain events trigger compliance workflows, actions call your existing systems directly. You can easily push data to your KYT platform, update case management queues, and log events in existing audit trails. In practice, this means a Kwala workflow can call Chainalysis KYT’s API to score a flagged transaction, POST the risk score to your Salesforce or ServiceNow case queue, and simultaneously log the event timestamp and transaction hash to your audit trail system all triggered by a single on-chain event, all completing within seconds. You define the chain of API calls in the workflow configuration. Kwala executes them in sequence on every qualifying event.
Regulatory tech Web3 solutions work best when they enhance your current stack rather than replace it. For teams operating across networks, understanding how cross-chain automation works helps design workflows to maintain visibility regardless of chain.
Why Enterprise Teams Are Automating Compliance Before July 2026
MiCA transition periods vary, but most end by July 2026. The Netherlands’ deadline passed in July 2025. Germany and Austria faced December 2025 cutoffs.
DeFi compliance tools that automate monitoring and routing give compliance teams leverage. They focus on judgment calls and edge cases instead of data wrangling. The cost of non-compliance under MiCA is concrete: penalties up to €5,000,000 or 3% of annual turnover, whichever is higher, for serious breaches. DORA operational resilience failures carry their own penalty structures. Against that liability exposure, the engineering cost of deploying Kwala compliance workflows is negligible.
Beyond penalty avoidance, automation creates audit confidence. Every workflow execution is logged with timestamp, event data, and action outcome. When a regulator requests evidence of your monitoring program, you produce structured logs rather than reconstructing a manual process from memory. That audit trail is not just useful under MiCA Article 68, it may be required.
Automated blockchain infrastructure for reporting now positions platforms for confidence as enforcement ramps up. The platforms building compliance automation now will operate confidently, while others struggle to catch up.
Frequently Asked Questions: Web3 Compliance Automation with Kwala
Does Kwala replace blockchain analytics platforms like Chainalysis?
No. Kwala handles event detection and workflow automation. It connects to analytics platforms via API calls, routing on-chain events for risk scoring and investigation.
Can I monitor events across multiple blockchains?
Each workflow monitors events from a single smart contract. For multi-chain compliance, deploy separate workflows per chain with outputs routing to unified dashboards.
How does Kwala handle the Travel Rule?
Kwala detects qualifying transfer events and triggers configured actions. Integrate with Travel Rule providers like Notabene via API calls within workflows.



 book a call with us
book a call with us