Is your backend infrastructure slowing your decentralized app (dApp) down? Relying on slow, expensive polling scripts or centralized servers means you’re always a step behind. In decentralized finance (DeFi), even a split-second delay can be costly – it could mean missing a transaction or, worse, facing liquidation from an online wallet. However, when your dApp monitors your smart contracts at the block […]
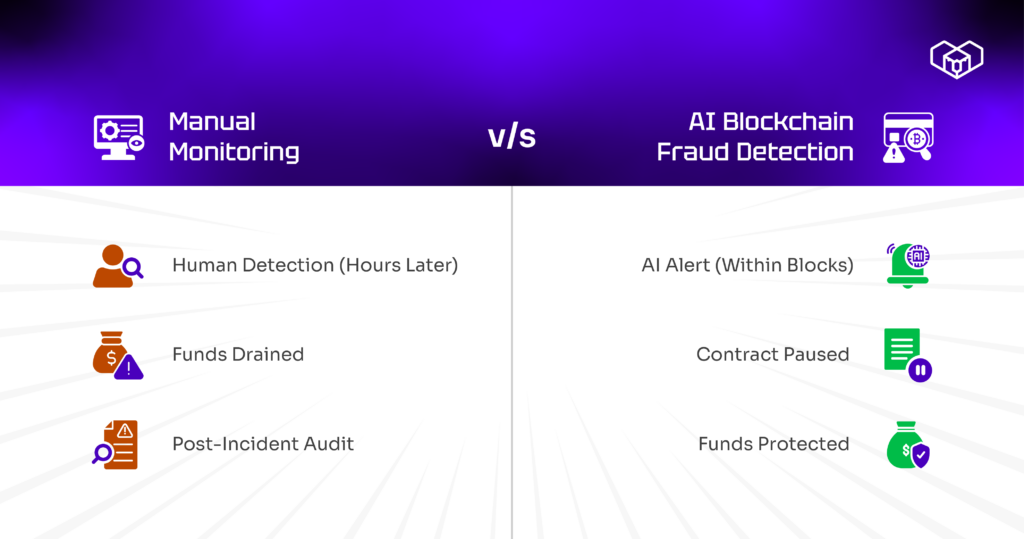
Read MoreBlockchain fraud detection in DeFi is a race against time. By the moment most teams realize something is wrong, funds are already drained and routed through mixers. Traditional monitoring cannot match the execution speed of automated exploits, which is why AI-powered on-chain alerts are becoming critical for real-time Web3 security automation.
This is for DeFi protocol teams, security engineers, and Web3 builders responsible for protecting user funds. The core problem is simple: manual monitoring cannot detect fraud fast enough to prevent losses. Blockchain fraud detection must operate in real time, not retroactively.
In fact, most protocols discover exploits the same way – someone on the team sees weird transaction volumes, investigates, and realizes the protocol just lost six figures. Or worse, a white hat researcher tweets about the vulnerability before you even knew it existed.
Traditional monitoring doesn’t work at DeFi speed. You can’t have someone watching dashboards 24/7, hoping to catch fraud before it happens. By the time humans analyze suspicious patterns, automated attacks have already executed and exited.
On-chain AI alerts completely change the timeline by detecting anomalies while attacks are still running. It triggers automated responses before damage compounds.
That is the difference between catching fraud in seconds versus hours determines whether you prevent losses or just document them. Let’s see how blockchain fraud detection works.
Why manual blockchain fraud detection always arrives too late
Blockchain fraud detection often fails not because the threat is invisible, but because the response is delayed. Ask any DeFi team that’s been exploited when they first noticed the attack. The answer is almost always “after it was already too late to stop it.”
How do you distinguish between sophisticated DeFi activity and the early signs of an exploit? Manual monitoring relies on humans recognizing patterns that don’t look right. But attackers deliberately design exploits to blend in until the final step.
Blockchain fraud detection faces a fundamental timing problem:
- Flash loan attacks complete in single transactions
- Oracle manipulation executes across blocks but finishes before anyone notices price discrepancies
- Reentrancy exploits drain contracts through recursive calls that look normal individually
- Multi-step attacks spread suspicious activity across different transactions to avoid detection
Speed matters more than anything else, and traditional smart contract monitoring options just don’t offer that.
Protocols that detect threats while attacks are still executing can pause operations before significant losses occur. Those relying on manual monitoring discover breaches hours later when funds are already gone.
How AI actually recognizes fraud patterns in real-time
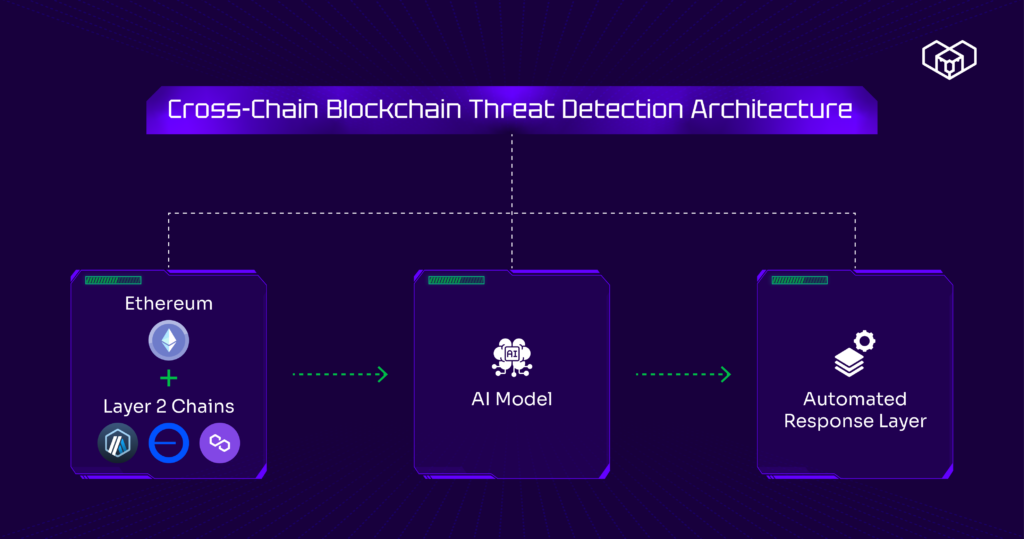
Web3 security automation using machine learning doesn’t work like rule-based systems that flag specific transaction types. It learns what normal looks like for your protocol, then immediately flags anything that deviates.
The model trains on your protocol’s transaction history – analyzing normal swap sizes, typical interaction patterns, expected gas consumption, time distributions. It builds a baseline of legitimate activity.
Then it watches every transaction in real-time. When something doesn’t match learned patterns, AI on-chain alerts trigger immediately.
Blockchain threat detection catches attack signatures that humans miss:
- Transaction sequences that don’t match any user behavior patterns you’ve seen before
- Contract interactions from addresses with suspicious funding sources
- Gas consumption deviating significantly from similar operations
- Price oracle updates creating instant arbitrage opportunities that exceed normal market movements
- Flash loan initiations from wallets that were funded minutes ago
What makes automated security Web3 systems effective is response speed. Detected threats trigger predefined actions within block confirmation times. Additionally, it pauses affected contracts, rejects suspicious transactions, and alerts security teams.
Teams implementing real-time risk management discover that automated detection responses happen at speeds manual monitoring cannot match.

Real exploits AI detection caught before they completed
DeFi fraud prevention through AI systems have stopped actual attacks mid-execution.
Oracle manipulation attempts get flagged when price feed updates create arbitrage windows that statistically shouldn’t exist based on market conditions. The system detects the price deviation and pauses trading before exploits can execute profitable swaps.
Flash loan attacks show distinctive signatures, such as borrowing maximum liquidity, executing complex transactions across multiple protocols, repaying within the same block. AI on-chain alerts recognize this pattern within block confirmation times and trigger circuit breakers before capital exits the protocol, preventing irreversible losses.
Reentrancy exploits generate unusual call patterns that consume gas differently than legitimate interactions. Smart contract monitoring detects recursive execution flows and automatically pauses vulnerable functions.
Governance attacks targeting treasury addresses get identified through sender analysis that flags wallets with suspicious funding sources. The transaction gets rejected before execution rather than discovered in audit logs later.
Automated responses prevented losses rather than just documenting how the exploit worked. That’s the difference between Web3 security automation and traditional monitoring.
Building automated fraud detection that actually works
DeFi fraud detection is configured by defining normal activity baselines and specifying responses when anomalies occur. The AI model continuously updates as your protocol evolves.
On-chain security alerts trigger based on confidence levels:
- High-confidence fraud executes automatic contract pauses to prevent further damage
- Medium-confidence anomalies alert security teams for immediate investigation
- Low-confidence deviations get logged for pattern analysis and model training
Web3 risk management improves over time as models learn from both false positives and actual attacks. Each flagged event refines detection accuracy for future threats.
Ready to move from reactive monitoring to real-time blockchain fraud detection?
Explore how Kwala’s AI-powered on-chain alerts automate Web3 security responses before exploits drain your protocol.
FAQs
How does AI-based blockchain fraud detection adapt to evolving attack strategies?
AI-based blockchain fraud detection adapts by learning from new behaviors in transaction flows, contract calls, and wallet interactions. Teams feed it labeled incident data, simulated attacks, and updated heuristics from post-mortems.
The model watches for feature drift in metrics like swap paths, approval patterns, gas spikes, and cross-contract call graphs. It also benefits from ensemble rules that ship quickly when a new exploit class appears. Continuous evaluation on recent blocks, plus shadow deployments that score traffic without triggering actions, helps tune thresholds and reduce blind spots before full enforcement.
Is automated fraud detection suitable for high-volume DeFi protocols?
Yes. Automated fraud detection is designed for high-volume DeFi when the pipeline is built for streaming data and low-latency decisions. Use event indexing and mempool listeners to avoid expensive full-chain scans. Partition monitoring by contract, function selector, and asset pair, then run detection in parallel workers.
Add rate-limited alerting and batching so operations channels stay usable during spikes. Tie actions to clear severity levels, such as notify only, pause a module, or raise a multisig task. Load testing on historical peak periods verifies throughput, lag, and failure recovery.
How do automated on-chain alerts integrate with existing protocol operations?
Automated on-chain alerts integrate by emitting structured signals into the same tooling your protocol already uses. Webhooks can post to Slack, PagerDuty, and incident systems. On-chain hooks can call a pause guardian, update a risk registry, or gate sensitive functions behind a circuit breaker. Many teams route alerts into a runbook engine that creates tickets, assigns owners, and starts a timed response checklist.
Integration works best when each alert includes the triggering transactions, affected contracts, recommended action, and confidence score. That metadata supports fast triage and auditable decisions.



 book a call with us
book a call with us